| To understand how bankers will prioritize their digital strategies in light of the tumultuous year that was 2020, CSI—a leading provider of fintech and regtech solutions—polled banking executives from around the country, representing 272 financial institutions from across the asset-size spectrum. The data from this survey was then collected and used to create an executive report to help bankers gain insight on the industry’s hottest topics and strategies. What Did Bankers Have to Say? It’s hardly surprising that, when asked about the future of the industry in CSI’s 2021 Banking Priorities Executive Report, digital transformation thematically unified every priority. While taking stock of their 2020 performance and assessing the year ahead, banking executives almost unanimously agreed: Digital use will likely not return to pre-COVID levels. Bankers began the survey by reflecting upon the past year with this question: please rate your bank’s response to the COVID-19 pandemic in the following areas on a scale of 1 to 5, with 5 being the highest. |
|
By Shane Ferrell, Vice President of Product Strategy - CSI
by Hunton & Williams LLP, reprinted with permission A Pittsburgh law firm has recently trained its sights again on community banks. This same law firm previously filed a number of class-action lawsuits against community banks: first, for alleged violations of the ATM fee-disclosure requirements in the Electronic Funds Transfer Act and, more recently, for alleged violations of the Americans with Disabilities Act (ADA) with regard to ATM-accessibility by disabled customers. In its latest attack on community banks, the law firm is sending demand letters to banks threatening litigation over the banks’ websites. The law firm contends the banks’ websites do not comply with the ADA because they allegedly are not accessible by disabled patrons.
ADA website-accessibility standards have not been issued by the federal government. In 2010, the US Department of Justice (DOJ) announced that was considering issuing regulations applying the ADA to websites. Originally, it was expected that DOJ would issue website-accessibility standards for places of public accommodation by the spring of 2014, [1] but the DOJ has now delayed issuing those regulations until 2018. Many have anticipated that ADA website-accessibility rules, if and when they are issued, will resemble the standards set forth in the Web Content Accessibility Guidelines (WCAG), which are promulgated by the Web Accessibility Initiative (WAI) of the World Wide Web Consortium. [2] As described by the DOJ, the “WAI has created recognized voluntary international guidelines for Web accessibility” which “detail how to make Web content accessible to individuals with disabilities.” Two weeks ago the National Association of Attorneys General (NAAG) sent a sign-on letter to attorneys general across the nation urging the implementation of chip and PIN technology in their states. The letter, to be sent to major card brands and issuers after those attorneys general added their signatures, sets forth the belief that chip and PIN should be the standard in the US and should be implemented without delay. This letter contains several mis-characterizations of security technology currently being used in the financial services industry, and directly contradicts the official positions of all four federal bank regulators, including the CFPB.
In response to this letter sent by the NAAG, CBI in conjunction with the Iowa Bankers Association and the Iowa Credit Union League have issued a statement to Iowa's Attorney General Tom Miller asking that he either decline to sign the above mentioned NAAG letter, or to withdraw his support if already given.
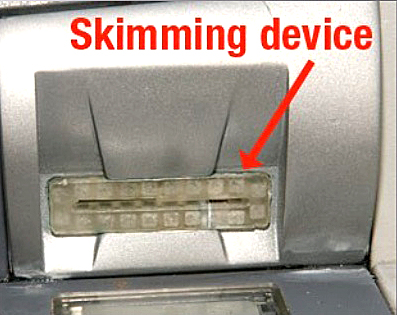
ATM card skimming is on the rise in the nation, and hit home in Iowa last week. Two men have been charged with using skimmer devices to capture bank account information at three locations around Des Moines. A skimmer device fits over the ATM's card reader slot and has its own memory chip to record the information on the card as it is swiped. Skimmers secretly record bank account data when a user inserts an ATM card into the machine. Criminals then can encode the stolen data onto a blank card and use it to access the customer's bank account. Skimmers also come in different colors like the green one used in Des Moines, or in a grayish color that would look similar to an ATM, making it hard to tell it's fake. Original card readers are usually concave in shape (curving inward), while skimmers are more convex (curving outward). The use of keypad overlays placed directly on top of the factory-installed keypad is a relatively new technique that takes the place of a concealed camera. Instead of visually recording users punching in PINs, circuitry inside the phony keypad stores the actual keystrokes. View the gallery below for examples of skimmers and keypads being used to steal account info from ATMs: DES MOINES, Iowa (February 5, 2015) — This week’s update to SHAZAM BOLT$, the mobile app offered by the SHAZAM Network, will give debit cardholders even greater access to their cash. New features include a person-to-person (P2P) money transfer service and an interactive ATM locator.
The app offers even greater value to community financial institutions looking to provide expanded digital services, particularly P2P features, to their customers. According to research firm Forrester, P2P activity is expected to grow to $17 billion in volume by 2019. The P2P money transfer feature allows SHAZAM BOLT$ cardholders to send money to other enrolled cardholders instantaneously. “While other P2P solutions use ACH to support their transactions, we’re using our SHAZAM debit rails, resulting in a much faster transaction,” said Terry Dooley, SHAZAM executive vice president and CIO. “A user can easily determine whether an intended recipient is enrolled simply by entering the recipient’s email address into the app.” SHAZAM also integrated GPS technology into the mobile app to help cardholders in the U.S. locate nearby ATMs. Users can confirm if the ATMs are surcharge-free Privileged Status terminals and get directions. Reposted from Iowa Banking Blog - Dickinson Mackaman Tyler & Hagen PC
In an important ruling in December 2014, the United States District Court for the District of Minnesota ruled in favor of banks suing Target over a December 2013 data breach, previously covered by this blog. Target had previously filed a motion asking the court to dismiss the banks’ lawsuit on the grounds that the banks had not stated a claim for which relief could be granted. Target attacked three claims asserted by the banks. Specifically, Target argued that the banks could not state claims for negligence, negligent omission, or a violation of Minnesota’s Plastic Card Security Act. The court addressed each of the three arguments in detail. First, the court concluded that the banks suing Target plausibly stated a rationale that Target owed each of the banks a duty. Under Iowa as well as Minnesota law, an entity is only liable for negligence if the entity first owed a duty to the party suffering injury. The court concluded that “Target’s actions and inactions—disabling certain security features and failing to heed the warning signs as the hackers’ attack began—caused foreseeable harm to [banks] . . . . .” As a result, the Court concluded that “[i]mposing a duty on Target in this case will aid Minnesota’s policy of punishing companies that do not secure consumers’ credit- and debit-card information.” The court’s conclusion was based in part of the fact that Minnesota has enacted a statute intended to safeguard the security of customer credit card information by limiting the retention period for the data.  Community bankers should ensure their processors are aware of the “Poodle” hack and to take steps to block the cyber-attack. Banks and other institutions are susceptible to the attack, which can intercept sensitive data used by website visitors. The name of the hack is an acronym for Padding Oracle On Downgraded Legacy Encryption. The good news for banks is that Poodle attacks are fairly easy to block. The first step for a company is to check its websites to see if they're vulnerable. There are a several free scanners that check for the presence of flawed encryption that allows it, such as https://www.poodletest.com. |
Community Banking NewsCurrent news, events, regulations and other information in banking, and at Community Bankers of Iowa. Stay Connected.
CBI Blog Archives
April 2024
Categories
All
|














 RSS Feed
RSS Feed